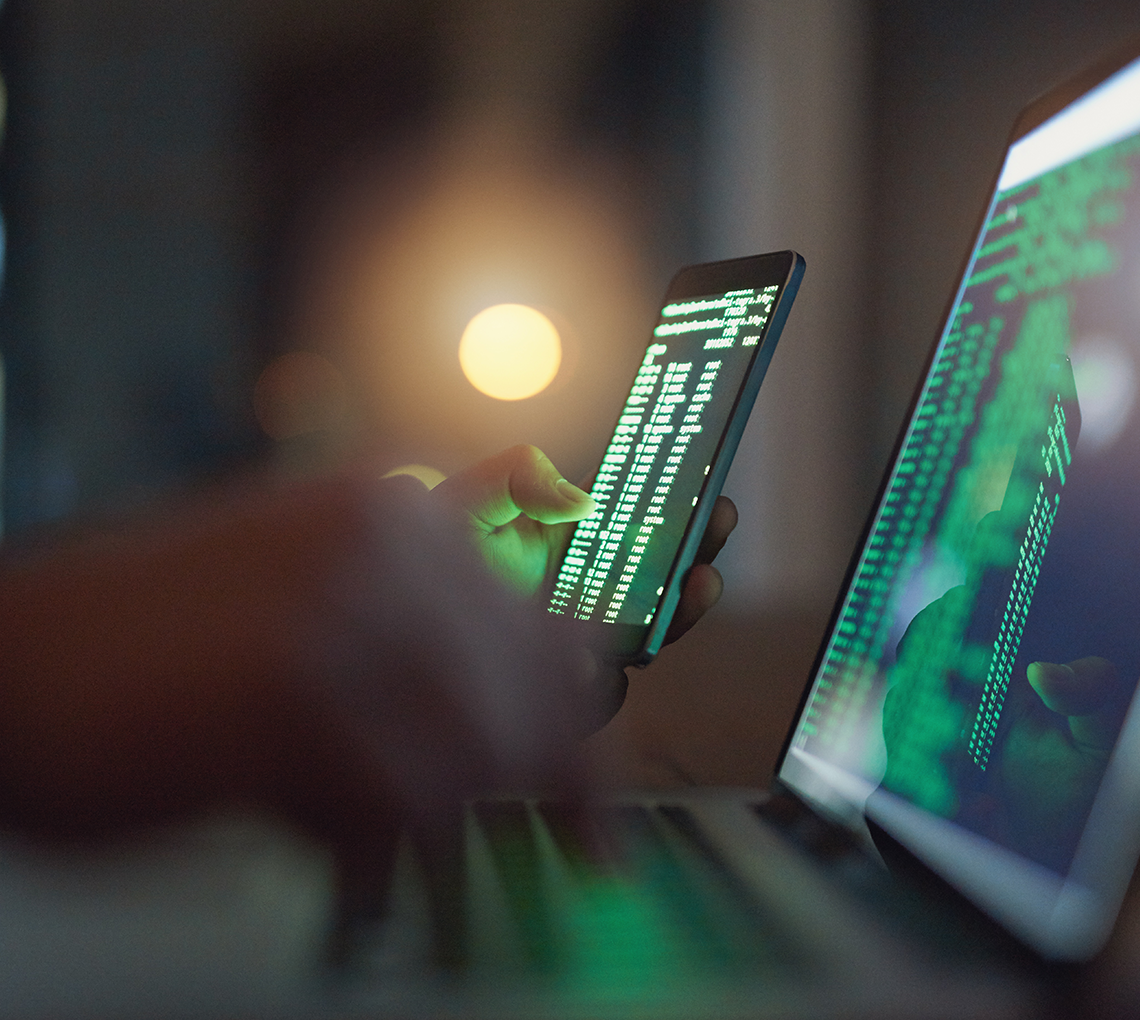
Having access to dependable data is crucial for achieving success.
Improving strategic business processes and minimizing risks begins with high-quality data. With Human Inference's software solutions, you can clean, match, and correct all your customer data, leading to more satisfied customers, better compliance, and increased customer interactions.
DataHub is a unique Master Data Management solution that comes with a powerful matching engine capable of recognizing and matching patterns as accurately as the human brain. It is a data quality and management solution that enables you to mitigate risks based on complete, accurate, and unique data. With DataPlatform, you can improve the quality of your contact data by cleaning it up, matching it for consolidation and duplicate reduction, and also matching it with sanction lists. All of this is achieved through natural language processing and fuzzy logic techniques.
[HIER KOMT DE HORIZONTALE LIJN]